We’ll be using Palo Alto Networks log forwarding for threat tagging in combination with dynamic groups to help block IP’s acting shady. As long as you know what kind of traffic you think should warrant a quarantine, you should have no problem dropping it as soon as it occurs.
- Open Object -> Log Forwarding
- Add or modify an existing log forwarding rule
You can use a single log forwarding for all your tagging rules, as well as syslog forwarding if you’d like to. - Press «Add» to add a new Match List.
- Select your log type, and a filter.
For the first example we’ll be using the URL filter log, and using a query that will tag anyone outside of Norway attempting to access the /wp-admin or /xmlrpc.php files.
As long as the filter is giving you the correct result when viewed in the URL filter log, you’ll be good.
If you press in the downward arrow on the right side of the Filter box, you can also use the Filter Builder to show you available fields as well as validating the output of your filter.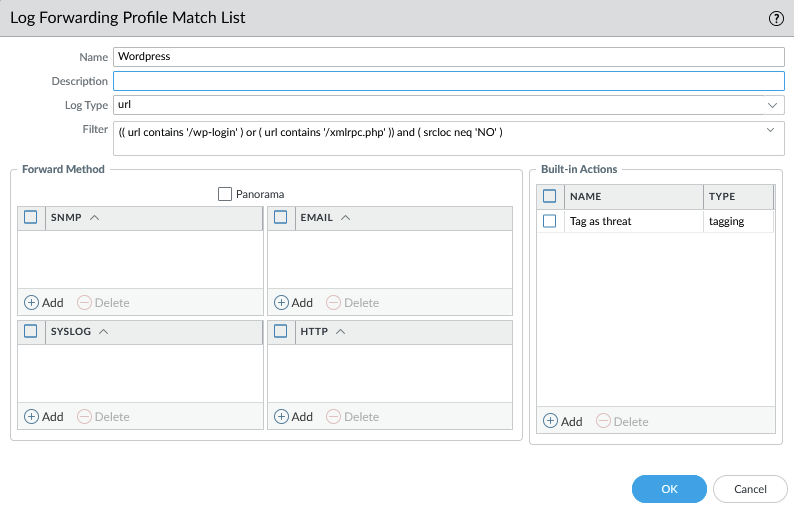
- Under Built-in actions, select tagging.
We’d like to set the source address as the target, this being the IP that will be given a tag. In my home lab I’ve got a single tag, but at work we’re using seperate tags for internal and external threats.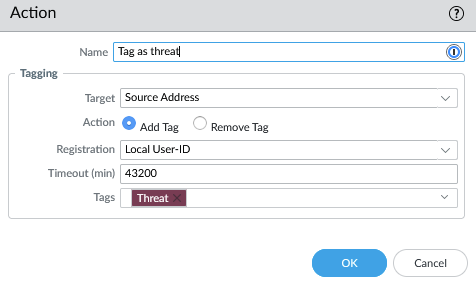
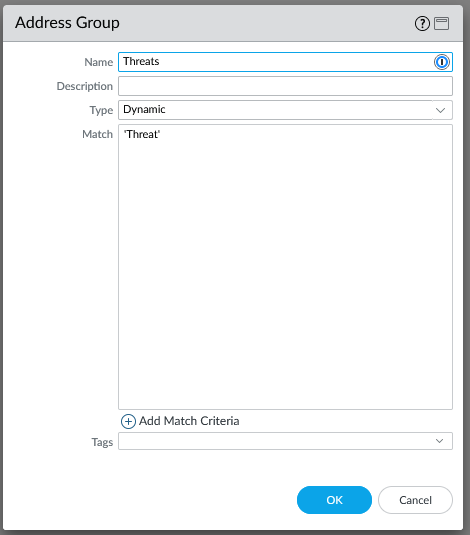
- With that done, head off to Objects – Address Group.
- Press Add to create a new dynamic group, set the match to ‘Tagname’.
- Go to Policies, add the newly created dynamic group to an inbound drop rule
Use different policies for different kinds of traffic, of course, but as the one we’ve just created is for Internet traffic, add it accordingly.
You might want to start with step 9, so you can see what populates first, and see if anything is tagged erroneously.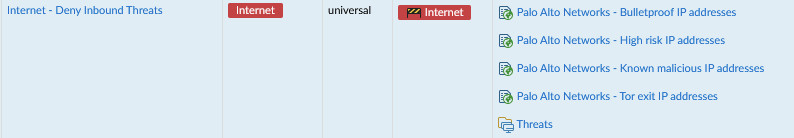
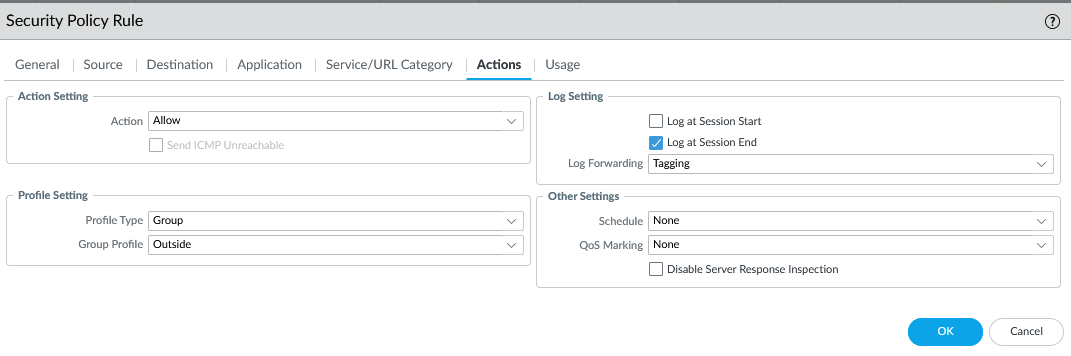
- Add the log forwarding rule to any applicable rule you have.
A couple of usefull log filters
Blacklist traffic going to high value targets if not coming from a trusted network:(( zone.dst eq Backup ) or ( zone.dst eq Management)) and ( zone.src neq Privileged )
Blacklist anyone triggering a medium or higher severity threat:( severity geq 'medium' ) and ( zone.src eq 'Internet' )
Adjust this to fit your network, of course.
Oh no, I blacklisted legit traffic and now people are yelling at me!
How do I fix this?
- Go to Objects -> Address Groups
- Find the dynamic group, and under «Addresses», click «More».
- Find the IP in question
- Press Unregister tags.
- Press Add, add the tag you’d like to remove (such as ‘Threat’) and press OK twice.
- Done, no need for a commit.
Further reading: